Check if your Linux machine is vulnerable to Copy-Fail exploit
Norm gets root with AF_ALG socket ( #CopyFail ).
https://cdn.masto.host/mastjohn1126com/media_attachments/files/116/513/861/295/418/841/original/de12e083654543f6.mp4
Because of this hack, access was given to Norm, to folders and files he was not supposed to have. He could copy them, modify them, or delete them.
Websites are now probably getting taken offline, or damaged because of this. Confidential information is being stolen. So many different problems could emerge from this hack. And it's been in place since 2017, so is it possible the hack has been used without a prior public release of this knowledge?
If you would like to check if your machine is vulnerable, here is the python code.
#!/usr/bin/env python3
import socket
import sys
def hex_bytes(x: str) -> bytes:
return bytes.fromhex(x)
def check_af_alg_aead():
print("=== AF_ALG AEAD reachability check ===")
# 1. Try to create an AF_ALG socket
try:
s = socket.socket(socket.AF_ALG, socket.SOCK_SEQPACKET, 0)
except OSError as e:
print(f"[OK] Could not create AF_ALG socket: {e}")
print(" AF_ALG is not usable from userspace on this system.")
return 0
print("[INFO] AF_ALG socket created.")
# 2. Try to bind to the AEAD interface used by the exploit
try:
s.bind(("aead", "authencesn(hmac(sha256),cbc(aes))"))
except OSError as e:
print(f"[OK] Could not bind to AEAD interface: {e}")
print(" The specific AEAD path used by the exploit is NOT available.")
return 0
print("[INFO] Bound to AEAD interface 'authencesn(hmac(sha256),cbc(aes))'.")
# 3. Try to set key and authsize (still non-destructive)
try:
s.setsockopt(socket.SOL_ALG, socket.ALG_SET_KEY,
hex_bytes('0800010000000010' + '0' * 64))
s.setsockopt(socket.SOL_ALG, socket.ALG_SET_AEAD_AUTHSIZE, None, 4)
except OSError as e:
print(f"[OK] Could not configure AEAD parameters: {e}")
print(" The full AEAD configuration path is not usable.")
return 0
print("[WARN] AF_ALG AEAD interface is reachable and configurable.")
print(" This strongly suggests the kernel path used by the exploit is available.")
print(" If your kernel version is known to be vulnerable, this system is likely exploitable.")
return 1
if __name__ == "__main__":
rc = check_af_alg_aead()
sys.exit(rc)This script (download as text file) does not hack anything, but checks if a machine is likely to be vulnerable. If you run this and it reports that your machine is vulnerable, I suggest you update your kernel. You might want to do that regardless.
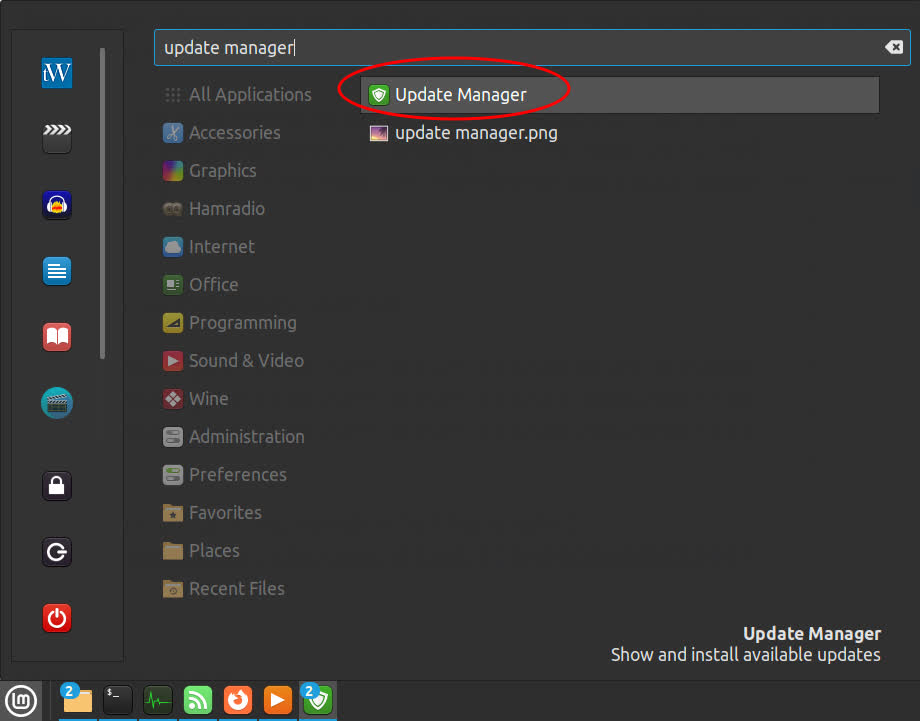
Linux Mint Update Manager
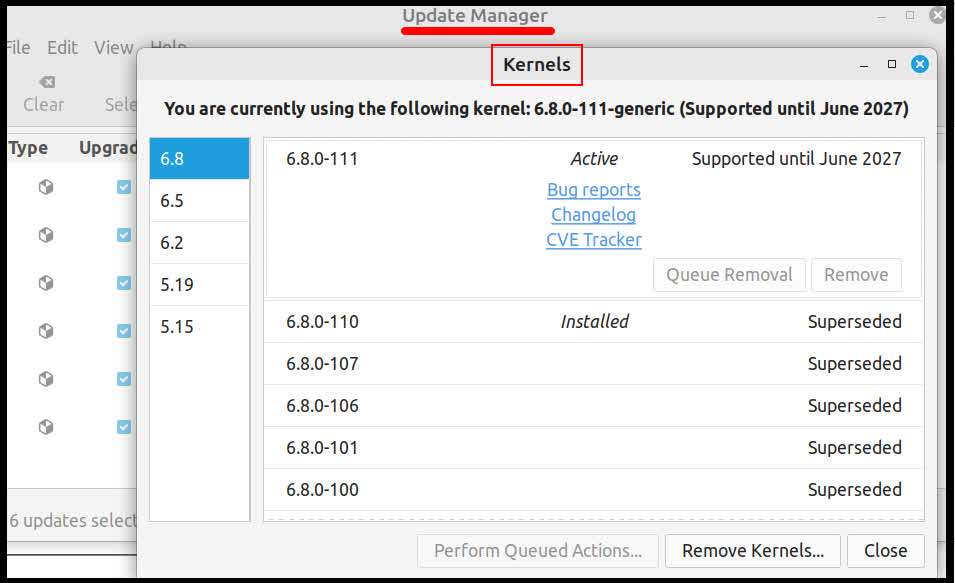
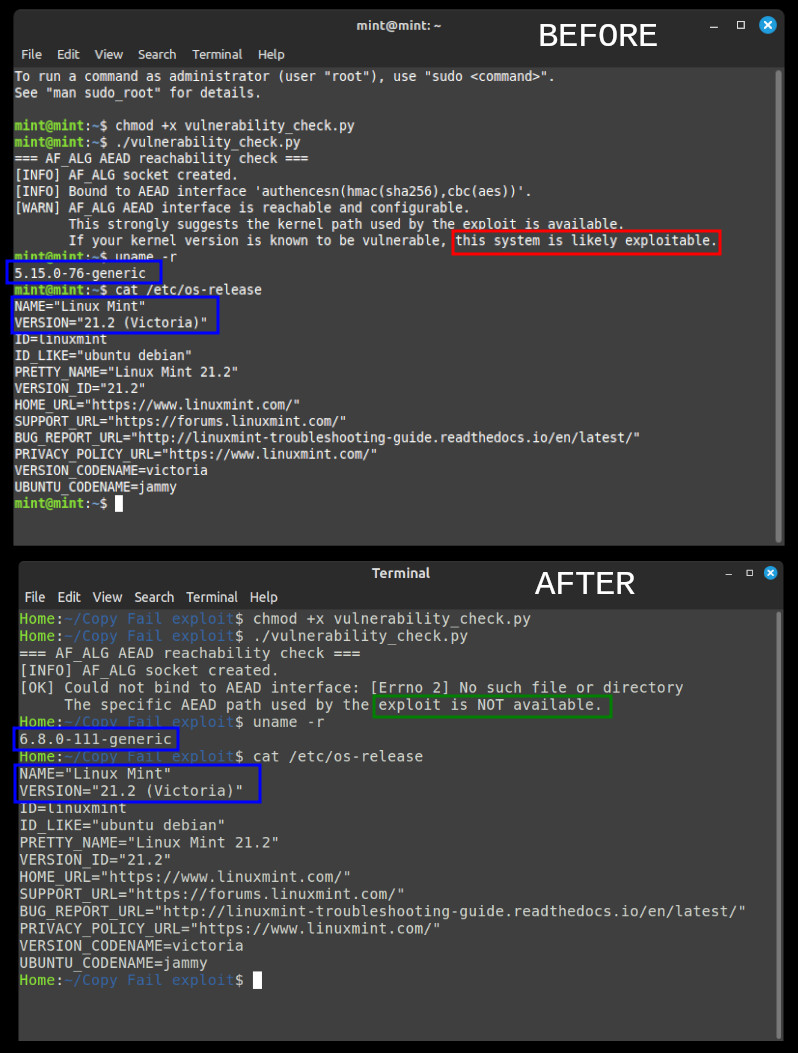
After I updated the kernel, the vulnerability was taken away.
This is a serious world-wide problem. I suspect many will (and already have) suffered loss from this Linux flaw. I've been praying to the Lord about it, asking Him to help us to not be victims to this hack or any other attack of the enemy. I have also been asking Him if this was an intentional backdoor added to Linux, or an unintended mistake.
How this vulnerability started....
https://mast.john1126.com/@Earl/116501814918450089
https://mast.john1126.com/@Earl/116511308620677281
https://mast.john1126.com/@Earl/116501746209673724
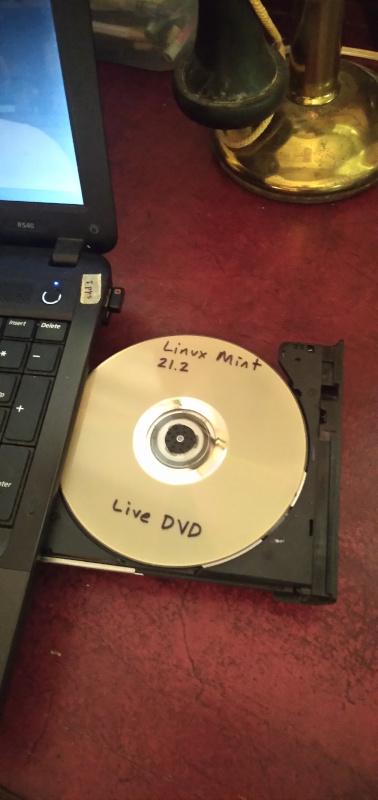
Linux Mint 21.2 is vulnerable to this exploit.
https://mast.john1126.com/@Earl/116496506898534473
Tags
CVE-2026-31431
May 3, 2026, 11:10:43 PM | by Admin